MNSM for Dummies
My buddy Chris Sanders has written an awesome book (Applied Network Security Monitoring: Collection, Detection, and Analysis) detailing the practice behind network security monitoring (NSM). In addition to being an incredibly astute security analyst and author, Chris is truly one of the nicest people I know - and someone who puts his personal beliefs into action (ex. all of the proceeds from his books go to charity).
As much respect as I have for Chris (and for other, lesser known folks who have written books about NSM) they all - unfortunately - have it wrong.
You see, according to them you’re - apparently - supposed to actually be DOING something about monitoring your network… Really? REALLY!?!?
How quaint.
Doing something to monitor your network is SO twentieth century. It’s time these authors dropped their throwback mentality and stepped into the era of Modern Network Security Monitoring (MNSM).
Chris and Richard and a whole lot of other people talk about these “packet” things like… well… like they’re something real. They encourage you to “capture” them, “log” them, or “monitor” them as if such meaningless activity will actually accomplish something useful. What balderdash!
I’m here to tell you that looking at the traffic on your network is nothing but a complete waste of your time. And time, as we all know, is money.
Why, pray tell, should we be expending time, effort, and money looking for these mythical “packets” when we have real work to do? I speak, of course, about advertising.
How can people know about the wonders of our sooper-dooper VPS hosting with cPanel / Parallels-Plesk / 100% Uptime Guarantee / Super-FAST SSD / 3TB transfer that you can stand up in 3 DAMN SECONDS FLAT for the low-low price of ONLYTHREEFRICKIN’NINETYFIVE a month if we spend our time monitoring our networks instead of advertising our NEW! LOWER! PRICES???
How can we possibly undercut those evil OTHER GUYS (that just lowered their price to ONLYTHREEFRICKIN’NINETYTHREE a month) if we spend money to actually monitor what’s happening on our network?
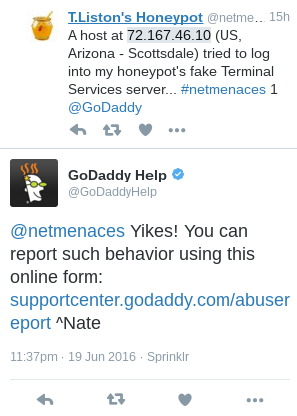
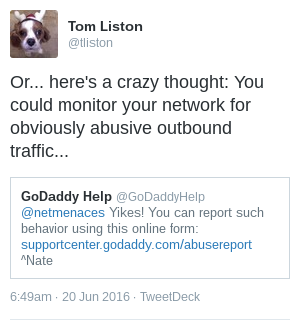
There is, however, some good news… Using the proven techniques of MNSM, we can leverage the awesome power of the Internet to monitor our network FOR us. Here’s how: Create an abuse@ email alias or - even better - a “report abuse” web page on your corporate site and simply kick back and wait.
Sure, we’re allowing any miscreant that can scrape together enough spare change to buy a Happy Meal™ to have their very own server on the Internet. Sure, a lot of them have larceny at heart or are clueless to the point that they’re going to use “password” for their password. Sure, that’s going to likely cause a LOT of abusive outbound traffic.
But we’re covered. Totally covered.
The Internet has our back. The folks out there who actually monitor their networks for attacks will let us know about the most egregious violators on our network. They are our NSM - and they’re free.
We just need to watch that email address (or the output from that web page) and when the complaints about a certain IP address reach a high watermark (or we’re feeling particularly frisky because we just lowered our price to ONLYTHREEFRICKIN’NINETYONE a month… suck it, evil OTHER GUYS) we can fire off an email to a client telling them to knock off the crap or we’ll ban ‘em.
Then we can go back to counting our money…
-TL
Tom Liston
Owner, Principal Consultant
Bad Wolf Security, LLC
Mastodon: @tliston@infosec.exchange
Twitter: @tliston
June 20, 2016